“Microsoft Pluton Hardware Security Coming to Our CPUs”: AMD, Intel, Qualcomm
by Dr. Ian Cutress on November 23, 2020 3:15 PM EST
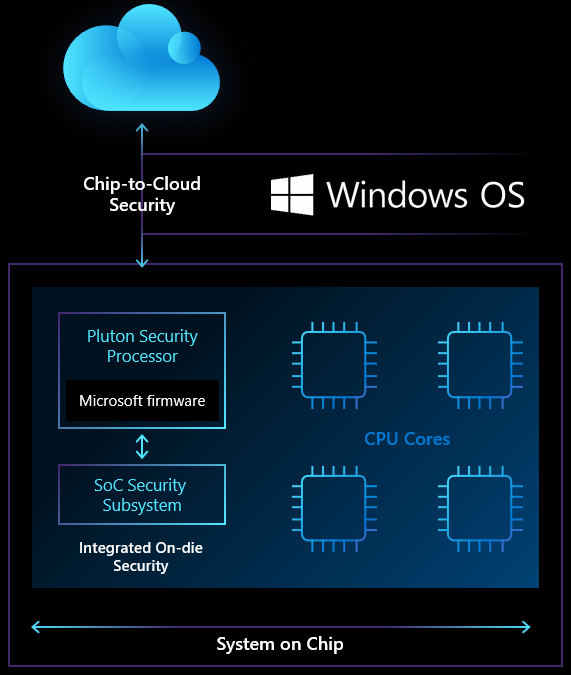
One of the key tenets of having good security is reducing how attackable your system is. This is what we call an attack surface – a system needs as few attack surfaces as possible, and as small as possible, to minimize any potential unwarranted intrusion. Beyond that, any additional security to detect and protect is vital. Both hardware and software can be used for that layer of additional security, and it becomes particularly important when dealing with virtualization, especially when it comes to virtual and physical attacks. In order to create a more unified system, Microsoft’s Pluton Security Processor, which works with Windows, is coming to the three major hardware vendors that implement the OS: AMD, Intel, and Qualcomm. What makes this different is that this is a physical in-hardware implementation that will be built directly into the future processors from each of the three companies.
Pioneered in both Xbox consoles and Microsoft’s Azure Sphere ecosystem, the Pluton Security Processor enables a full-stack chip-to-cloud security akin to a Trusted Platform Module (TPM). The TPM has been a backbone of server security over the last decade or more, providing a physical store for security keys and other metadata that verifies the integrity of a system. In the mobile space, a built-in TPM allows for other security verification, such as Windows Hello or Bitlocker.
Over time, according to Microsoft, a physical TPM module in these systems have become a weak point in modern security design. Specifically, gaining physical access to the system makes the TPM useless allowing for in-transit data hijacks or man-in-the-middle data pruning. Because a TPM is an optional addition to most server environments, that physical module-to-CPU data pathway becomes an important attack surface.
What the Pluton project from Microsoft and the agreement between AMD, Intel, and Qualcomm will do is build a TPM-equivalent directly into the silicon of every Windows-based PC of the future. The Pluton architecture will, initially, build an emulated TPM to work with existing specifications for access to the current suites of security protocols in place. Because Pluton will be in-silicon, it severely reduces the physical attack surface of any Pluton-enabled device.
The Pluton architecture seems to also allow for a superset of TPM features, perhaps to be enabled in the future. Microsoft highlights both the unique Secure HArdware Cryptography Key (SHACK) technology such that security keys are never exposed outside of the hardware environment, as well as community engagement such as what has been done through Project Cerberus, part of the Open Compute Project to enable root-of-trust and firmware authentication. We are told this is particularly important as it pertains to wide-spread patching issues.
All of the silicon vendors involved will have Pluton as the first layer of security – additional layers (such as AMD’s PSP) will go below this. From the three vendors, AMD has worked with Microsoft already on Pluton for consoles, so it should not be a big step to see Pluton in AMD consumer and enterprise silicon sooner rather than later, along with AMD’s other technologies such as Secure Encryption Virtualization. Intel stated that its long-term relationship with Microsoft should lead to a smooth Pluton integration, however the company declined to comment on a potential timeline. Qualcomm is the odd-one-out in a sense, as its cycles are a little different, but the company is quoted as stated that on-die hardware root-of-trust security is an important component of the whole silicon.
A number of parallels are being drawn between Pluton and Apple’s T2 security chip, which was moved inside the recently announced M1 processor.










27 Comments
View All Comments
Silver5urfer - Monday, November 23, 2020 - link
No thanks. M$'s own tablets like Surface are already riddled with enough Secure Boot and other garbage locks that block users from installing OSS like Linux distributions and on top you have Intel's cancer protection at PCH level which block BIOS unlocks or options for end users again to enable proper Undervolt and etc, with latest SGX issue on Intel CPUs most of the mobile machines couldn't even do a proper Uv. A big shame since out of box they have high voltage. M$'s own Defender is able to scan BIOS but user cannot do anything, thanks to their trusted secure boot garbage (It was hacked as well, Boothole vulnerability) and their UWP nonsense is even more crappy, DRM inbuilt into the damn OS itself (Xbox Gamepass and other junk, some OEM companies started to use that only and big corp too like Dell / Alienware and Intel).With more control slipping out of consumer devices and more privacy invading issues all over the place. I hope we can turn off this trash on day 1.
Hulk - Monday, November 23, 2020 - link
I agree completely.ballsystemlord - Saturday, December 12, 2020 - link
I third the motion.Alistair - Monday, January 3, 2022 - link
couldn't agree more, i'll take security, but not from these interested parties that care more about controlling you, not helping you be more secureKjella - Monday, November 23, 2020 - link
With Bootcamp going away on the Apple side it's no surprise that Microsoft is also looking to make a one-trick pony. I doubt any anti-trust case will stick when their main competitor isn't offering dual-boot anymore either.WaltC - Monday, November 23, 2020 - link
This article kind of collapses on the "gaining physical access" necessity for defeating TPM. Yes, *if you have physical access* pretty much anything is possible. It's "gaining physical access" that is the clincher, here...;) That's the *hard part* most often, imo.jeremyshaw - Monday, November 23, 2020 - link
The genesis for this project (at least for MSFT) was the Xbox, specifically the Xbox One... where physical access is the name of the game. Without physical access, the traditional game console model just doesn't work at all.beginner99 - Tuesday, November 24, 2020 - link
Gaining physical access can actually be the easy part and is a core part of "hacking" and doesn't require mad technical skills.philehidiot - Sunday, November 29, 2020 - link
Is this thing going to allow me to post? It says I'm spamming... I agree with beginner99.There is so much placed on the assumption that you can't get physical access to a system. I'm professionally trained in physical pen testing and I've trained in ethical hacking. Yes, certainly there are places where mad James Bond skillz are required and you'd need to be a state level actor (or an expensive industrial espionage firm using ex intelligence staff) to get in. That ain't me. But for most places, dressing up as a cleaner, courier or just wearing a damned suit will get you anywhere you need to go. A high vis is an all access pass if there's any work going on (and there always is in a large institution) and there are single button press, miniaturised card cloning devices available now.
Never, ever assume that your network will be protected by physical security. Because I guarantee you two things - the physical and cyber security people in an organisation rarely speak and even more rarely do they work together. And atop that, your physical security people are assuming their stuff is protected by the cyber security (in the case of electronic access control systems or networked CCTV systems) as well as vice versa. This is why so many places use broken RFID security and why the data travelling from RFID readers is (almost) universally sent in the clear, using the same protocol as since electronic access control systems were invented. Because physical and cyber don't work together.
philehidiot - Sunday, November 29, 2020 - link
I did an assessment on a large financial institution's external security a while back. A wifi networked camera was visible on a standard 802.11 2.4GHz scan and was labelled "thermal camera". Worse than that, you could tell where that camera was pointing so, without any effort at all, or risk of burning anyone, you can deauth it and sit and wait to see if security turns up, and thus ascertain the level of CCTV monitoring / diligence.Cyber and physical don't work together and each assume the other is doing their thing. If your network security is hinging on physical doing their job, I strongly suggest you audit it. All that means is walking around together, looking at each other's security and you'll soon find you each have a very different take on things. Audits like that need to be bidirectional and round table. You'll end up asking questions each other won't ask (like "can I take that card reader off the wall?" "why would you do that?" "to splice into the wires and collect the data" "whaaa? you can do that?" "uh yes" - and the end result is the tamper on those card readers actually gets connected. Or noting the locks on your cabinets are cheap and easily bypassed by anyone who has the skills to get that far, only to find that the physical guys keep a stock of high security locks and hasps they can fit with little to no spend from your budget).
Ramble over. I hope this helps someone see it from the other side.